4 Steps to Securing your Personal Data After a Breach
Protecting your personal data is a growing concern in our society. There is news of cyber attacks and data leaks being reported constantly and we are all potential victims.
Take the recent LinkedIn data breach for example, 92% of users on the platform were affected by that breach. While it is a terrifying reality that data breaches like this are projected to only increase, rest assured that there ARE steps you can take to keep your personal data as secure as possible.
Follow these 4 steps to secure your data in the event of a data breach:
1. Be in the Know
Stay informed by consuming cyber news from a trusted source. The sooner you know of data breach, the sooner you can act.
2. React Quickly
Be quick to react. As soon as you learn of a reported cyber attack against any organization you have an account with, begin to research to determine if you were affected by the breach and what type of data was leaked.
The website HaveIBeenPwned.com is a great resource for checking to see if your account data is affected. You simply enter your email address to view a report of data breaches containing that email with a brief description of the information that was leaked.
Do keep in mind that data breaches are not immediately updated, so if it is a new report, it may not yet appear on the site.
3. Take Action Depending on the Type of Data Leaked
As a rule, always update log-in credentials such as passwords in the event of a data leak. Other actions taken will depend on the type of information that was released.
-
- Find out what info has been breached.
- Change any exposed passwords.
- Switch from text-based MFA to an application app
- Remove your home address
- Freeze your credit
- Delete accounts you aren’t using
4. Be Prepared
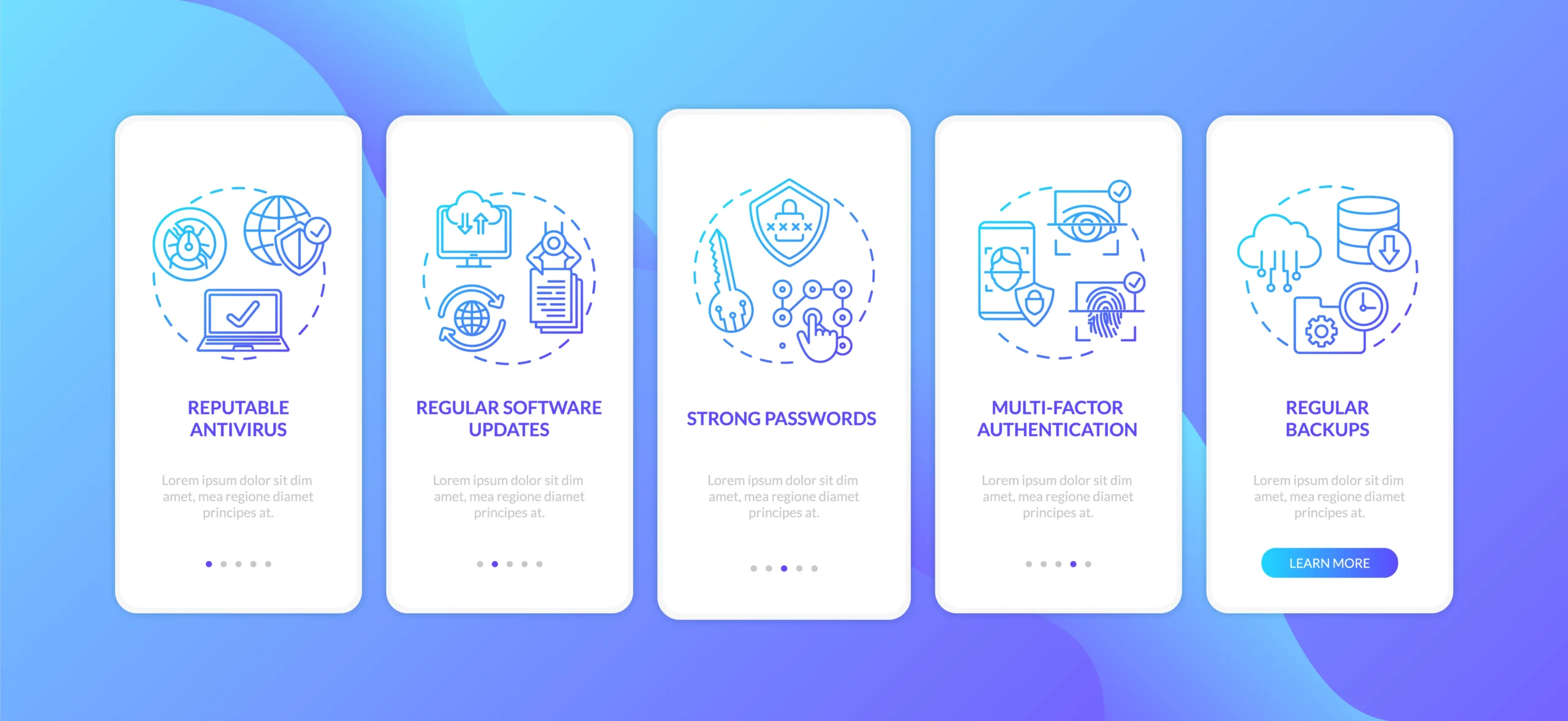
Not all cybercriminals will use your data for harm immediately after at attack. Some may even wait years. However, continued good cyber hygiene practices can help you to be prepared.
What is Cyber Hygiene?
Cyber hygiene refers to the steps that users of computers and other devices can take to improve their online security and maintain system health.
Cyber hygiene means adopting a security-centric mindset and habits that help individuals and organizations mitigate potential online breaches.
Common cyber hygiene problems
-
- Security breaches
- Data loss
- Out-of-date software
- Older antivirus
Bottom Line
Ultimately, cyber hygiene means developing a protective routine to keep your personal and financial information secure when using your computer or mobile device, both at work and at home.
Finding a trusted technology coach can help businesses and their employees keep their data safer. Contact PCA Technology Solutions to learn how we can partner with you.