If you run a Dallas construction company, cybersecurity is probably not the first thing on your mind when you show up to work. You’re managing bids, coordinating subcontractors, keeping projects on schedule, and making sure your crews have what they need. Security is something you deal with when something breaks (if you deal with it at all).
That mindset is understandable. Running a Dallas construction business in a market as competitive and fast-moving as Dallas means your attention is constantly pulled toward the next deadline, the next project, the next client. Cybersecurity may seem more like an IT issue than a business issue.

Unsure where your biggest cyber risks are?
PCA helps internal IT teams and growing organizations make the right technology decisions.
However, the truth is that cybercriminals don’t think that way. They view Dallas construction companies as high-value, high-opportunity targets because they manage sensitive project data, execute massive wire transfers, and have lean IT staff that seldom have time for proactive protection. They don’t wait for you to be prepared. They’re already trying to find a way in.
The good news is that awareness is the first step, and you’re already taking it. Understanding the threat landscape specific to DFW construction firms is what separates companies that respond to breaches from companies that prevent them.
The Numbers Don't Lie: Construction Is Under Attack
This is not a theoretical risk. Construction was the most targeted industry, with an average of 226 incidents annually, according to ReliaQuest’s Annual Cyber-Threat Report. Cyberattacks on construction enterprises increased between 2023 and 2024, with ransomware and phishing attacks rising by 41% and 83%, respectively. That is an industry under attack, not gradual development.
Think about what that means in practical terms. A ransomware attack doesn’t just lock up your files. It can freeze project management software, shut down communication with subcontractors, block access to bid documents, and halt billing. For a firm in the middle of an active build, every hour of downtime has a dollar figure attached to it.
And the threat isn’t limited to ransomware. Phishing emails targeting project managers, credential theft aimed at accounting teams, and business email compromise schemes designed to redirect wire payments are all on the rise across the construction industry. Cybercriminals have studied how construction firms operate, and they’re exploiting the gaps.
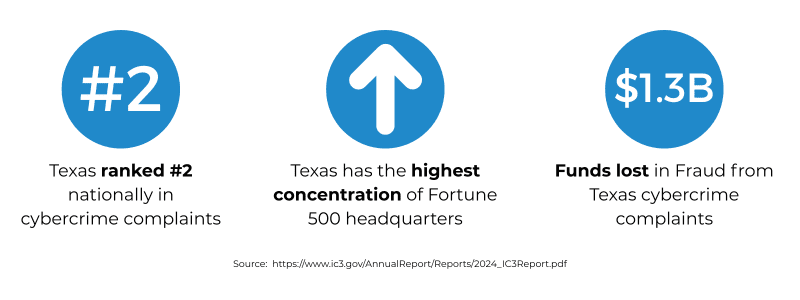
For DFW contractors, the stakes are even higher. With one of the fastest-growing construction markets in the country, Dallas firms are managing larger project volumes, more subcontractor relationships, and greater digital complexity, all of which expand the attack surface. The more projects you’re running, the more entry points exist for an attacker to exploit.
Dallas-Fort Worth is home to billions of dollars in active commercial, residential, and infrastructure development. That level of economic activity makes it a high-priority target. Cybercriminals follow the money, and right now, a significant amount of it is flowing through DFW construction firms. If your Dallas construction company is growing, winning larger contracts, or expanding its subcontractor network, your risk profile is growing with it.
Why Dallas Construction Companies Are Prime Cyber Targets
Construction companies are a prime target for cyberattacks. They handle financial plans, bid documents, proprietary designs, and sensitive client data, all of which are highly valuable to cybercriminals.
Attackers using ransomware exploit this urgency because they know that even short-term disruptions can halt entire work sites, delay multimillion-dollar projects, damage reputations, and increase the likelihood that companies will pay ransoms promptly.
Additionally, the subcontractor network amplifies your exposure. Your vulnerabilities are compounded by the inadequacies of third-party partners, many of whom lack basic security training. In a market like Dallas, where projects rely on extensive subcontractor networks, this risk compounds quickly.
There’s also a regulatory gap. For most commercial contractors, cybersecurity risks in construction go largely unregulated. Cybercriminals are aware that, in the absence of external pressure, investments in controls such as multi-factor authentication, monitoring, and backups lag behind actual threats.
What We're Seeing in the Field
Phishing, credential theft, and business email compromise (BEC) attempts to target construction companies commonly. In an instance where, according to the U.S. Department of Justice, Texas construction companies were targeted by a criminal conspiracy that registered domain names closely resemble those of legitimate firms. The perpetrators sent emails impersonating company employees to deceive clients into wiring payments to fraudulent bank accounts. The scheme ran from 2016 to 2018 before federal authorities intervened.
The initial breach often isn’t some intricate hack. Sometimes, it’s the absence of layered security measures or a simple lack of user vigilance that allows it. Attackers aren’t targeting the largest companies, they’re targeting the most accessible ones.
When backups are compromised, organizations are almost twice as likely to pay the ransom and face a recovery bill eight times higher. A backup strategy that hasn’t been hardened may not save you when it matters most.
The Small IT Team Problem
Lean IT teams in construction are overburdened with maintaining systems, assisting field workers, overseeing vendors, and handling pressing problems. There isn’t much left for proactive security or staying up to date with new threats.
When a single team is responsible for everything, security becomes reactive. Attackers look for blind spots brought by patching delays, inconsistent controls, and missed alerts. Without interfering with regular business operations, a co-managed IT solution can help close the gap.
What Dallas Construction Leaders Should Do Next
You don’t have to solve every problem at once. Start with the basics.
Make identification and access a top priority. A compromised credential is the first step in most breaches. Controlled access and multi-factor authentication are essential, not optional. Understanding why MDR security matters is a strong next step.
Harden your backups. Your recovery strategy needs to be tested and separated from your main network because attackers specifically target backup systems. Remote monitoring and management tools can help keep backup integrity continuously validated.
Know what a breach actually costs. Many leaders underestimate the full financial impact, it goes well beyond ransom payments. Downtime, legal exposure, notification costs, and reputational damage add up fast. The real cost of a data breach is often far higher than firms expect.
Don’t go alone. With a co-managed IT model, Dallas construction companies can bring in outside expertise for security, monitoring, and strategic planning while keeping the internal team focused on day-to-day operations.
Dallas construction boom isn’t slowing down, and neither are the threats. Managing construction cyber risk means treating cybersecurity as part of operations, not a competing priority.
The question isn’t whether your firm is a target. At this point, the data is clear: it is. The question is whether you’re prepared.

Ted Clouser
President | CEO
Ted Clouser, President and CEO of PCA Technology Solutions, began his journey in technology at the age of 16 when he launched his own computer business. In 1996, he joined PC Assistance of Little Rock, and in 2018, he and his wife, Stephanie, purchased the company. Within a year, Ted rebranded it as PCA Technology Solutions, expanding its offerings to new markets. Under his leadership, PCA has become a trusted name in cybersecurity, IT consulting, professional services, managed IT services, and Voice-Over-IP (VoIP) solutions. Ted’s passion for both people and technology drives his commitment to delivering innovative IT solutions that empower businesses. Married since 1998, Ted and Stephanie have two adult children: Alexis and Ethan. Ted’s dedication to his family and his industry exemplifies his forward-thinking approach and leadership.
Connect:

What’s New in MS Teams: 10 Must Know 2025 Features
Microsoft Teams has rolled out a suite of updates in 2025, designed to enhance user experience and workplace efficiency. These changes, based on valuable user feedback, help streamline workflows, improve communications, and make everyday tasks feel more seamless. ...

How Business IT Solutions Drive Growth and Saves Costs
Let's face it: Running a business isn't cheap. Between rent, salaries, marketing, and everything else in between, it's easy to look at business IT solutions as "just another expense." But what if we shifted that perspective completely? What if we told you that the...

Cloud Token Theft: How to Detect and Prevent Attacks
Imagine this: You log into your cloud account as usual, but unknown to you, a cybercriminal has already stolen your authentication token. They now have the same access you do, without needing your password. Scary right? This is the reality of token theft, a rising...