What is SOC, SOAR, SIEM, MDR, and XDR?
Cybersecurity evolves rapidly, and acronyms such as SOC, SIEM, SOAR, MDR, and XDR are common in boardrooms and vendor presentations. What do these terms mean, and how do they work together to protect your business?
As an IT service company, we often encounter confusion about these related terms. Each serves a distinct function. Some are technologies, others are services, and some combine people, processes, and platforms. Together, they form a security architecture designed to defend against evolving cyber threats.
Let’s clarify each term and explain how they work together in practice.
Understanding the Modern Security Stack
Modern cyberattacks are complex. Attackers may use phishing, move laterally within networks, escalate privileges, and exfiltrate cloud data. No single security tool can effectively monitor or respond to all these activities.
That’s where SOC, SIEM, SOAR, MDR, and XDR come in. Each serves a role in detection, response, automation, monitoring, and governance. When properly integrated, they provide visibility, speed, and resilience.
What Is SOC?
A Security Operations Center (SOC) is the centralized function responsible for monitoring, detecting, investigating, and responding to cybersecurity incidents.
A SOC is an operational model that integrates security analysts, defined processes, and supporting technologies, in contrast to a single product.
The SOC operates 24/7, reviewing alerts, validating threats, containing attacks, and analyzing root causes. It acts as the nerve center of cybersecurity operations. When security tools generate alerts, the SOC team evaluates them and determines the appropriate response.
From a strategic perspective, the SOC provides oversight and accountability. Without this structure, alerts can go uninvestigated, and risks can increase.
What Is SIEM?
Centralized visibility is based on Security Information and Event Management, or SIEM.
SIEM systems collect log data from servers, firewalls, endpoints, cloud platforms, identity systems, and other infrastructure components.
This aggregation of logs enables correlation analysis. Instead of focusing on isolated incidents, SIEM analyzes patterns across systems to find suspicious activities. For example, unusual login attempts, authorization changes, or network anomalies may trigger high-risk alerts.
Because SIEM stores and organizes historical data, it is especially useful for forensic investigations, compliance, and auditing. However, the primary function of SIEM is detection and alerting. It detects possible dangers, but until it is coupled with other tools, it does not react to them automatically.
For organizations asking what is SOC, SOAR, SIEM, MDR, and XDR, it helps to think of SIEM as the visibility engine. It answers the question:
“What is happening across our environment?”
Get Expert IT Guidance Today
What Is SOAR?
Security Orchestration, Automation, and Response (SOAR) build on what SIEM starts. If SIEM detects threats, SOAR helps respond to them often automatically.
SOAR platforms integrate with multiple security tools and execute predefined workflows known as playbooks. These playbooks standardize and automate repetitive tasks such as gathering contextual data, isolating infected devices, disabling compromised accounts, or creating incident tickets.
The value of SOAR lies in speed and consistency. Manual investigations take time, and large volumes of alerts can overwhelm security teams. Automation reduces response time and ensures standardized actions during incidents.
SOAR augments analysts by automating repetitive tasks, allowing human expertise to focus on advanced analysis and threat hunting. In mature environments, SOAR can significantly reduce Mean Time to Respond (MTTR), a key cybersecurity performance metric.
What Is MDR?
Managed Detection and Response (MDR) is a cybersecurity service, not merely technology.
MDR combines advanced detection technologies with experienced security experts who monitor environments 24/7.
Organizations collaborate with an IT service company that provides round-the-clock monitoring, proactive threat hunting, incident validation, and guided or direct reaction rather than creating an internal SOC from the ground up. Endpoints, networks, and cloud services are regularly examined by MDR providers for signs of compromise that automated techniques could overlook.
The human layer of MDR is an advantage. Technology produces data, but skilled analysts decipher trends, distinguish genuine dangers from false positives, and take prompt action. MDR provides security without the need to hire a complete security crew for businesses with a small workforce.
When discussing what is SOC, SOAR, SIEM, MDR, and XDR, MDR represents the managed operational capability that helps bring everything together.
What Is XDR?
Extended Detection and Response (XDR) is an evolution in threat detection.
Traditional security tools often operate in silos. Endpoint tools monitor devices, network tools analyze traffic, and email security platforms inspect messages independently.
These data sources are combined into a single platform by XDR. To identify complex, multi-stage attacks, it correlates with telemetry from endpoints, networks, cloud environments, identity systems, and email platforms.
The key advantage of XDR is context. Instead of generating multiple disparate alerts, XDR links related signals into a single, high-confidence incident. This reduces alert fatigue and improves detection accuracy.
For example, a phishing email click, unusual endpoint activity, and suspicious authentication attempts might appear harmless individually. XDR connects them, revealing a coordinated attack.
By combining detection and response capabilities, XDR provides a unified framework for security visibility and action.
How These Technologies Work Together
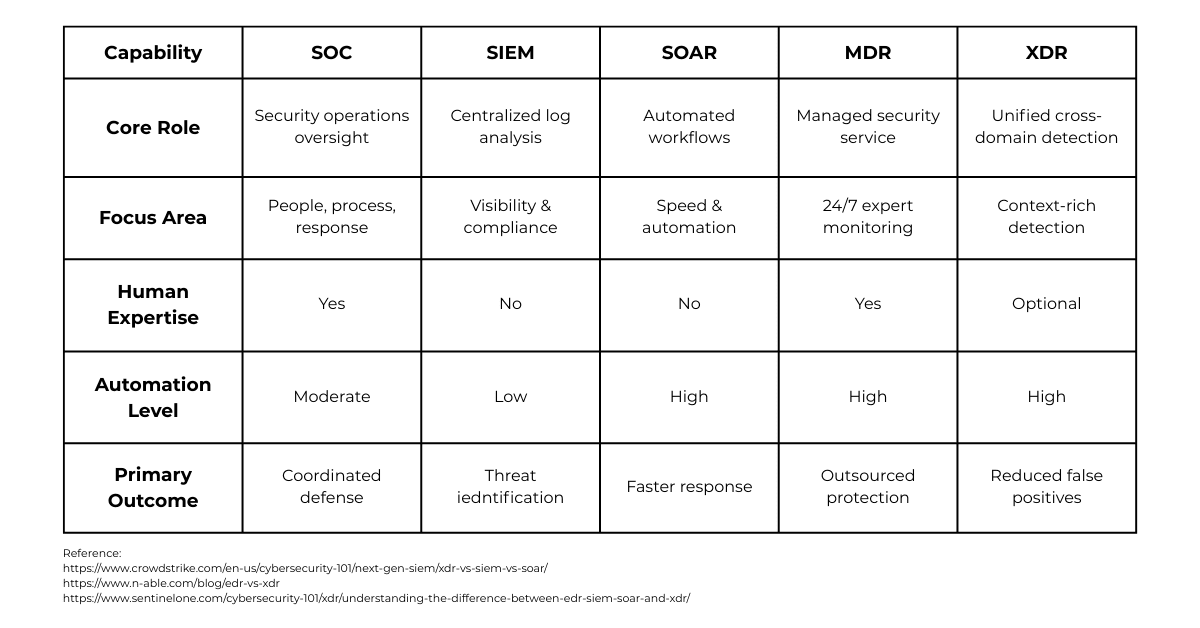
Each component serves a distinct purpose, and integration is what gives them power. Log aggregation and analysis are the focus of SIEM. Cross-domain threat detection is the major focus of XDR. Responses are organized and automated using SOAR. The SOC creates a plan and oversees security operations. MDR offers expert-led, managed threat response and monitoring.
Modern cybersecurity strategists do not choose one solution over the others. Instead, they layer these capabilities together.
Risks arise when key elements are missing:
- Visibility without response creates gaps.
- Automation without oversight creates inconsistency.
- Detection without human expertise can miss critical nuances.
An effective security architecture aligns technology, people, and governance. That alignment is where an experienced IT service company provides measurable value.
What Matters Most Strategically
The discussion should move from definitions to results when assessing SOC, SOAR, SIEM, MDR, and XDR. The real goal is to reduce risk while improving detection speed and response accuracy.
Internal capabilities, risk tolerance, operational complexity, and regulatory needs must all be evaluated by organizations. To establish visibility, some can start with SIEM. For instant, round-the-clock coverage, others might give priority to MDR. To improve automation and cross-domain detection, more developed settings might use XDR and SOAR.
Cybersecurity maturity is not achieved by purchasing tools alone. It requires intentional architecture, continuous optimization, and executive alignment. Technologies should strengthen business resilience, not complicate it.
Final Thoughts
Building a contemporary, robust security strategy requires an understanding of SOC, SOAR, SIEM, MDR, and XDR. Each plays a distinct but complementary role:
SOC provides oversight and strategy.
SIEM delivers centralized visibility.
Response time is accelerated by SOAR.
MDR offers managed expertise.
XDR enhances contextual detection across systems.
When combined, they produce a multi-layered defense mechanism that can handle changing threats.
As an IT services company, our priority is not just implementing these technologies but aligning them with long-term business goals. We assist companies in creating, implementing, and overseeing cutting-edge security architectures that lower risk, speed up response times, and match cybersecurity with corporate objectives. Because building confidence, consistency, and control in an increasingly complicated digital ecosystem is more important for effective cybersecurity than chasing acronyms.
If you’re evaluating your current security posture or planning your next step, let’s start a strategic conversation.
Book a cybersecurity strategy call today and let’s build a smarter, stronger defense together.

Sean Tappe
Executive VP of Operations | PCA Technology Solutions
Sean Tappe is the Executive Vice President of Operations at PCA Technology Solutions, a role he has held with distinction. Sean’s journey with PCA began in 2008 as a Network Engineer. Through his dedication, expertise, and commitment to excellence, he quickly rose through the ranks within the organization. In his current role as Executive Vice President of Operations, Sean brings a unique blend of technical prowess, strategic vision, and a deep-rooted passion for exceptional customer service. He is known for his meticulous attention to detail, thoughtful approach to problem-solving, and deliberate decision-making process. Sean’s leadership style is characterized by a steadfast commitment to thorough research, enabling him to make informed and impactful decisions that drive PCA’s continued success.
Outside of his professional pursuits, Sean is an avid advocate for community engagement and giving back. Sean enjoys time with his wife and four children, spending time with friends, leading worship at church, and playing various sports and games. Living by the personal motto, “Here to serve,” Sean actively volunteers his time and expertise to various charitable initiatives, reflecting his commitment to making a positive impact beyond the realm of technology.
Enhanced Security with Remote Monitoring and Management
In today's digital world, the line between convenience and vulnerability has become incredibly thin. Businesses of all sizes (yes, even small ones) face growing cybersecurity threats every day. From ransomware to phishing attacks, no company is immune. That's where...

What’s New in MS Teams: 10 Must Know 2025 Features
Microsoft Teams has rolled out a suite of updates in 2025, designed to enhance user experience and workplace efficiency. These changes, based on valuable user feedback, help streamline workflows, improve communications, and make everyday tasks feel more seamless. ...

How Business IT Solutions Drive Growth and Saves Costs
Let's face it: Running a business isn't cheap. Between rent, salaries, marketing, and everything else in between, it's easy to look at business IT solutions as "just another expense." But what if we shifted that perspective completely? What if we told you that the...

