Blog Library
Library of information-filled blogs written by PCA contributors.
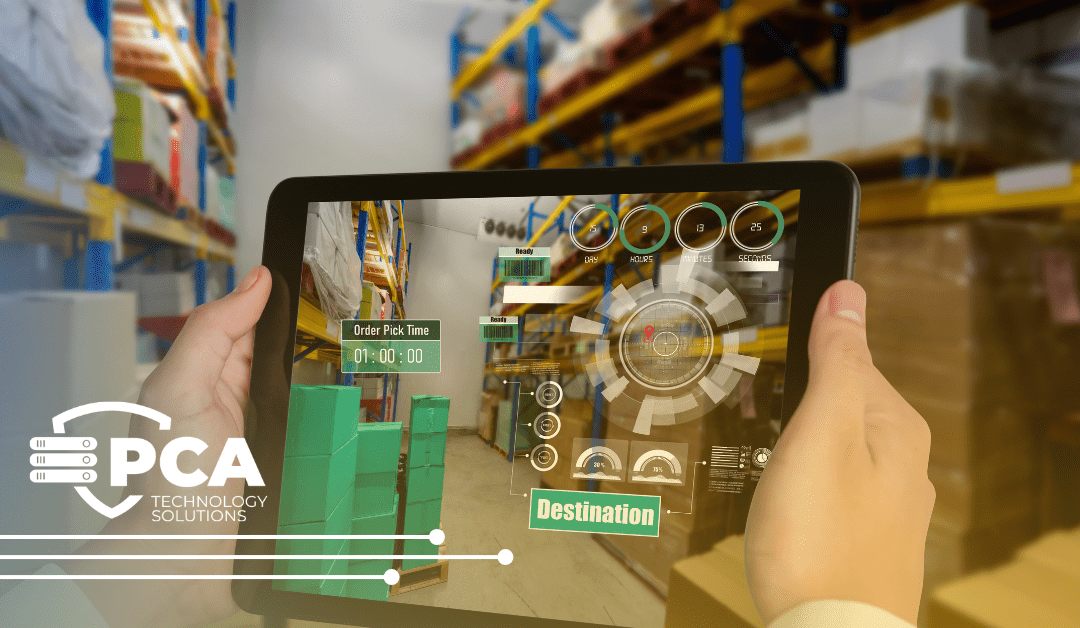
10 Ways Freight Management is Transformed by Digital Technology
Did you know? Inefficient freight management costs businesses billions each year. Problems like delayed shipments, lost inventory, and poor planning don’t just annoy customers—they eat up profits. But there’s good news: digital technology is fixing this! With tools...
Latest Blogs
Benefits of Using a Technology Provider for Procurement Needs
Managing the procurement of IT hardware, software, and services can be complex and time-consuming. This is where partnering with a trusted technology provider can be a game-changer.
10 Most Common Small Business Technology Mistakes
Ten common technology mistakes small businesses often make, which can lead to lost data, security breaches, decreased productivity, and wasted money.
Top Tips for Safer Online Shopping
Cybercriminals live for this time of year when we spend time online shopping the latest deals on holiday gifts. Read our top tips for a safer shopping experience!
6 Reasons to Skip Black Friday Sales for Your Business Technology Purchases
Black Friday sales are super enticing. Explore 6 compelling reasons to consider a more thoughtful and strategic approach to your business technology purchases.
Co-Managed IT vs. Full Service: What’s The Difference?
How do you determine whether your business needs full-service IT management, or if you need co-managed? We can help determine the best fit for your business.
“We Just Can’t Afford It”
All salespeople have heard this objection, “We just can’t afford it.” But, it’s so important to really calculate ALL of the costs associated, as John describes.








